Introduction:
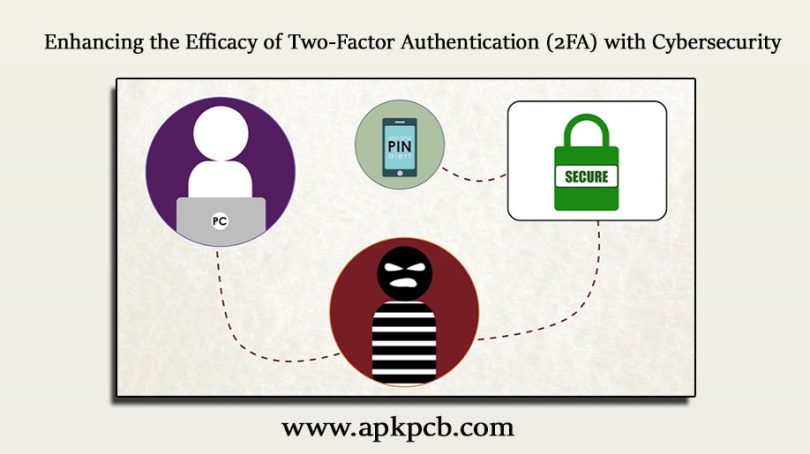
Strong security measures are necessary to secure sensitive information in the digital age, where data breaches and unauthorized access are commonplace. A strong method to increase security by providing an additional layer of verification is two-factor authentication (2FA). Cybersecurity is essential for bolstering 2FA and assuring its effectiveness against changing cyber threats. This essay will look at how cybersecurity affects the effectiveness of two-factor authentication.
Encryption and Secure Communication:
Transmission of 2FA codes or credentials must be protected using cybersecurity measures like encryption and secure communication protocols. Data is encrypted so that it can’t be read by anybody else, making it harder for anyone to intercept or decipher. The connection between the systems and devices involved in the 2FA process is kept secure by cybersecurity by using strong encryption techniques.
- Protecting the Authentication Infrastructure:
Authentication systems, servers, databases, and other components of the underpinning infrastructure that underpins 2FA must all be protected from potential weaknesses and exploits. To reduce the risks related to illegal access or manipulation of the authentication infrastructure, cybersecurity experts deploy security controls such as access controls, intrusion detection systems, and regular security audits. Cybersecurity precautions help to maintain the integrity and dependability of 2FA by protecting the infrastructure.
- User Education and Awareness:
Users are educated and made more aware of the value of 2FA thanks in large part to cybersecurity efforts. Users must be knowledgeable about the advantages of 2FA for their security and be able to use it effectively. Cybersecurity experts run awareness campaigns, offer training resources, and share best practices to equip users with the information they need to adopt 2FA successfully. Cybersecurity encourages the adoption and usage of 2FA by educating users about potential dangers, attack vectors, and protective measures.
- Protection against Social Engineering Attacks:
Cyber attackers frequently use social engineering strategies to target human weaknesses and get beyond security measures, such as 2FA. Attacks such as spear-phishing, phishing, and impersonation attempt to fool victims into disclosing their login information or granting access to their devices. By spreading knowledge about social engineering tactics, putting email filtering systems in place, and carrying out simulated phishing exercises, cybersecurity plays a critical part in thwarting such attempts. By strengthening user knowledge and resilience, cybersecurity measures lower the possibility of successful social engineering attacks that may undermine 2FA.
Why Two-Factor Authentication (2FA) Can Be Challenging:
While 2FA offers significant security benefits, there are certain aspects that warrant attention. Let’s explore some of the reasons why 2FA may be considered less advantageous in certain scenarios.
- User Convenience and Adoption Challenges:
The possible negative effects on user convenience are one of the main issues with 2FA. Having to go through the extra step of identification verification can be a hassle, especially when you need access right away. There is a chance that some users will become frustrated or unwilling to utilize 2FA if they must consistently submit additional verification codes or use physical tokens. To effectively use 2FA, it is necessary to balance security and user comfort.
- Dependency on Additional Factors:
A password or other piece of information from the user’s knowledge is generally combined with a physical item from the user’s possession, such as a smartphone or token, in two-factor authentication. This method improves security but adds a dependence on outside variables. The ability to access an account may be compromised if a person loses their physical device, forgets their password, or runs into technological difficulties. To properly handle such events, contingency preparations, and user assistance systems must be in place.
Protecting Against Cyber Attacks:
Cyberattacks have the potential to do serious harm and interfere with daily business. The following tactics can be put into practice to help defend against various cyberattack vectors:
- Strong and Unique Passwords:
Selecting strong, complex passwords will help you avoid using the same password on several accounts. Use a combination of uppercase, lowercase, numbers, and special characters. Consider using a password manager to create and store passwords securely.
- Frequently Updated Software and Patching:
Keep all software, including operating systems, programs, and plugins, up to date with security updates. Regularly check for updates and apply them as soon as feasible to close known vulnerabilities.
- Firewalls and Network Segmentation:
To keep an eye on and manage incoming and outgoing network traffic, use firewalls. To separate sensitive systems and reduce the possible impact of a breach, you should also think about segmenting your network.
- Anti-Malware Protection:
Install reliable antivirus and anti-malware programs on all hardware. Keep the software definitions current and run routine scans to find and get rid of malicious software.
- Employee Training and Awareness:
Informing staff about malware, social engineering, and phishing are common cyber threats. The importance of adhering to security best practices should be emphasized as you teach people to spot and report suspicious activities.
Solutions to Cybersecurity Threats:
Preventive measures and incident response tools must be used in concert to address cybersecurity threats. Here are a few defenses against prevalent cybersecurity threats:
- Social engineering and phishing
Use email filtering programs to identify and stop phishing attempts. Conduct regular awareness campaigns to inform staff members of the warning indications of phishing emails and other social engineering tricks. Develop a culture of doubt and double-check dubious requests via different avenues.
- Ransomware Attacks:
Take regular backups of your important data and keep those copies offline or in the cloud. To avoid ransomware encryption, keep offline backups. To recognize and stop ransomware attacks, implement tight access controls, segment networks, and use advanced threat detection technologies.
- Data Breaches:
Protect sensitive data by using encryption techniques both during transmission and while it is at rest. Implement access restrictions and routinely check user permissions to ensure that only individuals with the appropriate access rights can access sensitive information. Make an incident response strategy so you can act swiftly to stop data breaches.
- Insider Threats:
Use behavior analytics and user monitoring to spot any odd or suspect employee conduct. Apply the least privilege principle to ensure that staff only have the access privileges they require. While upholding strict security measures, cultivate a culture of transparency and trust.